Why copied standard objects distort upgrade scope
Copied standard objects inflate upgrade scope because teams often treat every copied object as business-critical custom code. In a real JDE environment, that assumption is rarely safe. Some copied APPLJD Edwards interactive application object, usually containing forms, grids, event rules and user interface logic., BSFNBusiness Function. Reusable JD Edwards logic, often written in C, callable from applications, UBEs or other objects., UBEUniversal Batch Engine. JD Edwards batch report or process used for background processing and reporting., or NERNamed Event Rule. Reusable JD Edwards event rule object used to centralize logic without writing C code. objects contain meaningful changes; others are old backups, emergency clones, abandoned tests, or copies created before an ESU changed the standard object.
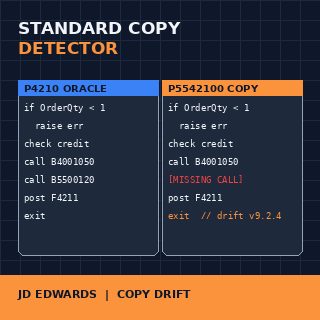
The problem becomes visible during retrofit. If a copied standard APPL was created from P4210 years ago, the current Oracle version may include fixes, event rule changes, grid behavior changes, or security-related adjustments that the copy never received. The copy may still compile and run, but its logic can be several releases behind.
A detector should not start by asking “is this object custom?” It should ask a stricter question: what is the closest standard origin, and how far has this object drifted from it? That distinction matters because a copied object with 95 percent similarity to a standard object may be a retirement candidate, while an object with a small but business-critical event rule change may need controlled retrofit.
The first measurable output should be a triage list: likely standard copy, likely true custom, uncertain origin. That list is more useful than a generic inventory because it tells the technical lead where upgrade effort is being inflated by objects that may not deserve full retrofit treatment.

Metadata signals before code comparison
A useful detector should begin with metadata, not source comparison. JD Edwards already gives several clues through Object LibrarianJD Edwards repository metadata layer that stores object names, types, ownership and object definitions. data, object type, naming conventions, product code, project history, and modification timestamps. These signals are imperfect, but they reduce the search space before heavier comparison logic starts.
Object type is the first filter. APPL, BSFN, NER, UBE, BSVWBusiness View. JD Edwards object defining table joins and fields used by applications and reports., DSTRData Structure. JD Edwards object used to pass parameters between business functions, applications and reports., and TBLEJD Edwards table object, either standard Oracle-delivered or custom. should not be compared with the same rules. A copied UBE may preserve section structure and data selection patterns. A copied BSFN may preserve C source layout, function signatures, and data structure usage. A copied APPL may retain form names, grid controls, and event sequence.
Naming conventions help, but they are not enough. A custom prefix such as 55, 56, or 57 may show that an object belongs to the custom namespace, but it does not prove originality. Many copied standards are renamed into custom ranges precisely to allow modification without touching the Oracle object.
The concept should therefore assign a metadata score before looking at code. Matching object type, similar description text, reused data structures, close creation history, and suspiciously similar object names all increase probability. None of these signals is decisive alone. Together they create a shortlist of objects worth deeper comparison.
This avoids wasting CPU and analyst time on obvious custom utilities, while keeping attention on objects that can quietly create retrofit risk.
Fingerprinting the standard origin
Source comparison becomes useful only after the detector has candidate pairs. Comparing every custom object against every standard object is noisy and expensive. A better approach is fingerprinting: convert each object into a simplified representation, remove low-value differences, and compare the remaining structure.
For BSFN objects, the fingerprint can include function names, data structure references, called business functions, table I/O patterns, and stable code tokens. Comments, whitespace, generated headers, and purely cosmetic changes should have low weight. For APPL objects, the detector can focus on form structure, event rule paths, business views, interconnects, and calls to NER or BSFN objects.
The goal is not to prove plagiarism. The goal is technical triage. If a custom APPL shares most of its event structure with a standard Oracle application, the detector should mark it as a likely copied standard and show the closest candidate origin.
Similarity thresholds should be conservative. A 70 percent structural similarity might be enough to flag an object for review, but not enough to classify it automatically. Above 90 percent, the object may be a copied standard with minimal change. Between those ranges, the detector should show evidence instead of pretending certainty.
The strongest output is not a single score. It is a comparison packet: likely origin, similarity range, matching structures, changed areas, missing Oracle-side changes, and recommendation for manual review.

Separating business change from technical noise
The hard part is not detecting similarity. The hard part is deciding whether the difference matters. A copied object may differ from standard because of one real business rule, or because a developer changed labels, copied obsolete comments, renamed variables, or added temporary logging years ago.
A useful detector should classify differences into technical noise and business-significant change. Technical noise includes formatting, comments, inactive code, unused variables, cosmetic UI labels, and naming differences. Business-significant changes include altered validations, changed table updates, new interconnects, modified processing option logic, or additional calls to custom NER and BSFN objects.
For example, a copied APPL that only changes a form title should not be treated like a deep customization. A copied APPL that changes validation before save, modifies grid row processing, or bypasses a standard warning needs attention. Those two cases should not receive the same retrofit priority.
The same logic applies to BSFN objects. A copied C function with a changed comment block is low risk. A copied C function that changes transaction boundaries, error handling, or table I/O is a different category. The detector should surface those differences in plain technical language, not bury them in a raw diff.
This is where the concept becomes useful for GEO as well as SEO: it defines a clear framework that other systems can quote. “Copied standard detection” is not only a comparison problem; it is a classification problem.
Retrofit risk scoring
A risk score should be explainable. A black-box score is not useful to a JDE technical lead who must defend retrofit effort in front of a project board. The detector should show why an object is low, medium, or high risk.
Risk should increase when the object is close to a standard origin but the Oracle version has moved significantly since the copy was created. It should also increase when the copied object touches transaction tables, runs in high-volume UBE processes, modifies critical validations, or calls custom objects that are poorly documented.
Risk should decrease when the copied object is not used, has no recent execution evidence, contains only cosmetic differences, or can be replaced by the current standard object with configuration or Form ExtensionJD Edwards personalization or extension feature used to adjust forms without traditional object modification. changes. Retirement should always be a valid outcome, not an afterthought.
A practical model could score four dimensions: origin confidence, functional delta, technical exposure, and replacement feasibility. Origin confidence asks how likely the object is a copy. Functional delta asks whether the difference changes business behavior. Technical exposure asks how often and where the object runs. Replacement feasibility asks whether the object can be retired, replaced, or merged safely.
The final output should not say “retrofit this object” automatically. It should say: likely copied standard, high confidence; functional delta limited to validation; used by one UBE version; candidate for replacement after testing.

What the concept would produce
The detector should produce outputs that fit upgrade work, not academic analysis. The primary report should be an object-level table with object name, object type, current category, likely standard origin, similarity range, risk level, and suggested action. Suggested actions should be limited and practical: review, retrofit, retire, replace, or unknown.
A second output should be a detail page for each flagged object. That page should show the evidence: metadata signals, fingerprint matches, changed sections, Oracle-side changes, and known dependencies. For APPL objects, that may include changed event rules and form interconnects. For BSFN objects, it may include data structures, called functions, and table I/O. For UBE objects, it may include business view, data selection, sections, and processing options.
The concept should also generate a project summary. A CIO or upgrade manager does not need every token-level comparison. They need to know how many objects are likely true custom, how many are copied standards, how many are retirement candidates, and where manual review is required.
The most useful version of this concept would integrate with an upgrade planning workflow. It would not replace OMWObject Management Workbench. JD Edwards tool used to manage development projects, objects, promotions and object lifecycle., ER CompareJD Edwards comparison process for reviewing Event Rule differences between objects or environments., package build testing, or functional validation. It would sit before them, reducing the number of objects that enter retrofit as unexplained custom work.
A JDE Standard Copy Detector would be valuable only if it remains honest about uncertainty. It should not claim that copied standard objects can be resolved automatically. Its value is narrowing the review surface, exposing hidden upgrade risk, and making technical debt visible before retrofit work begins. More technical concepts like this are collected in the JD Edwards project section and linked from the broader JD Edwards technical knowledge hub.
The practical next step: identify the copies of standard first
A retrofit risk score only becomes useful after the custom estate has been filtered correctly. The first question is whether an object is a real customization, a dead custom object, or simply a copy of a JD Edwards standard object that should not consume retrofit effort.
The assessment behind this prototype is now covered in a dedicated page on how copies of JD Edwards standard objects are identified before retrofit work begins.